Cyber Security Services
IoT Device Pentest
Elevate your IoT security strategy with our comprehensive pentest, where added value meets uncompromising cybersecurity for a connected future.
Human Touch
Passionately Resolute
Broad Capability
Global Experience
Multi Language Support
Added Value
Unleash the full potential of your IoT ecosystem with our IoT Device Pentest service. Going beyond conventional testing, we meticulously assess the security of your connected devices, identifying vulnerabilities and ensuring a resilient IoT infrastructure.
IoT Device Pentest
What to Expect with our IoT Device Pentest Service
Our expert pentesters simulate real-world scenarios, providing actionable insights to fortify against cyber threats. From device authentication to data integrity, our service offers a thorough examination, guaranteeing not just compliance but robust security.
Uncover vulnerabilities in your Smart Devices and fix them quickly
Internet connected devices can expose entire infrastructure to external and internal cyber threats.
Secure them now.
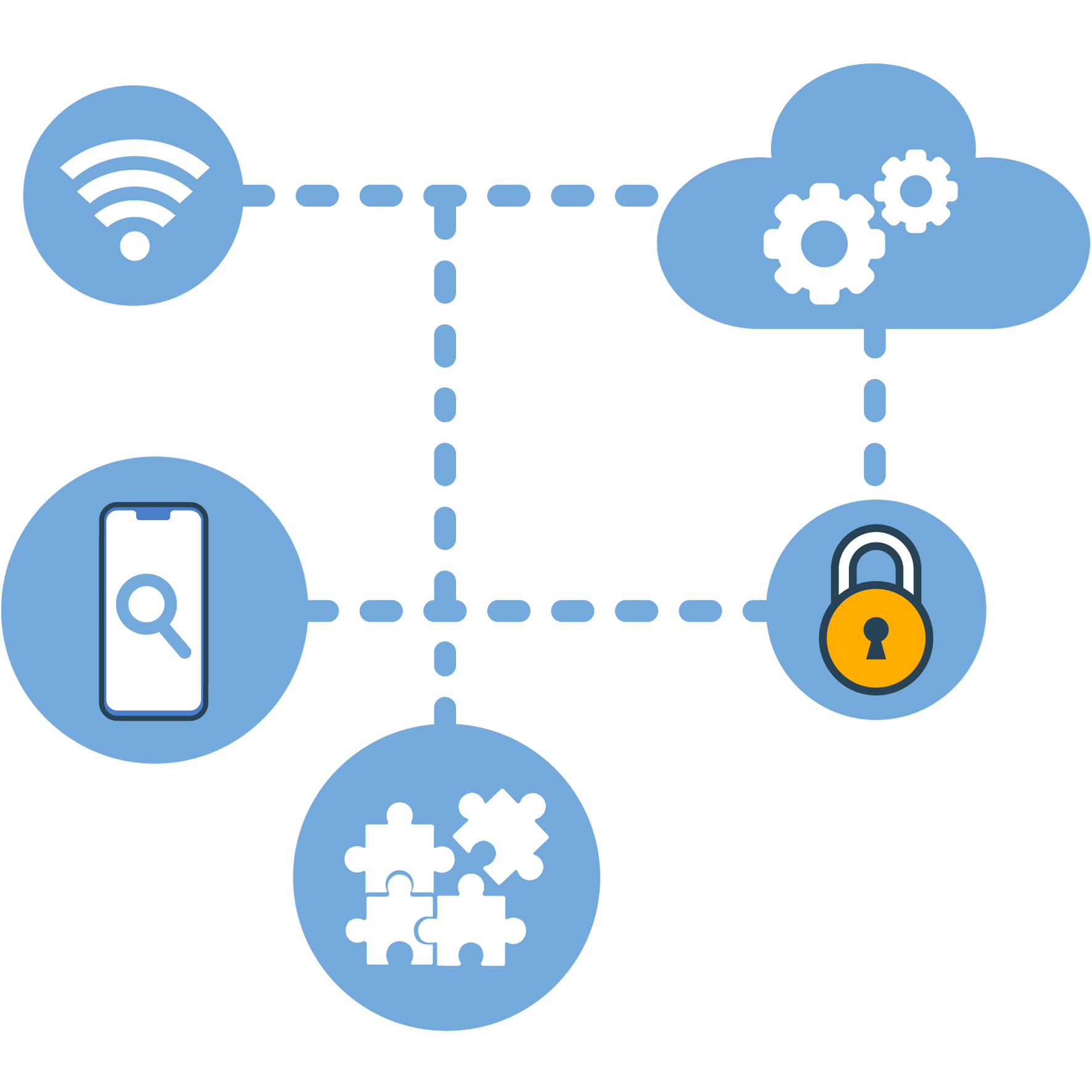
Our approach to IoT, Smart Devices pentest includes Hardware, Software and Server assessment.
Firmware Reverse Engineering
- Reverse engineering firmware binaries
- Binary exploitation
- Encryption analysis
- Bypass obfuscation techniques in use
- Debugging binaries to gain sensitive info
Application Pentesting
- Android, Cloud and Web vulnerability testing
- Input Validation: SQL Injection, Malicious Input acceptance, Command Injection
- Buffer Overflow, File Upload, Business logic validations, Error handling/ Info Leakage, Session management, Log tampering
- Data storage vulnerabilities
Server side Testing
- Identify potential for denial of service (DOS) attacks
- Vulnerabilities specific to web servers: Directory Traversal, Command injection, Remote code execution, SQL injection, Sensitive file exposure, Web server miss configuration exploitation
- API/Webservices testing: authorization, IDOR, Injections and exploits, API business logic bypas like skipping payments, API missconfigurations
- Radio communication reversing for proprietary protocols
Hardware based exploitation
- Exfiltration of Sensitive data from memory: applications store username, tokens, passwords, encryption keys, unscripted sensitive data.
- UART, JTAG, SWD ports exploitation
- Flash memory chips to detect a possibility to dump firmware.
- Logic bugs sniffing and bus tampering
- External peripheral devices: headphones, antennas etc.
Step into the future with confidence by securing your IoT ecosystem through Scorpion Circle’s IoT Device Pentest. Beyond traditional assessments, our meticulous evaluation delves deep into the security infrastructure of your connected devices, ensuring not only their immediate protection but also fostering resilience against evolving threats. By choosing our IoT Device Pentest, you are not just conducting routine checks; you are investing in the longevity and robustness of your IoT ecosystem, positioning it to thrive in the dynamic landscape of technological advancements.
At Scorpion Circle, we believe in the synergy of innovation and security. Our IoT Device Pentest is not merely a security measure; it’s a strategic initiative to harmonize innovation with robust protection.
By selecting Scorpion Circle, you’re opting for a partner dedicated to empowering your organization with the knowledge and strategies needed to navigate the complexities of IoT security.
Choose the bridge between innovation and security.
Choose Scorpion Circle!
Request More Information
Interested in knowing more about our company and Blockchain Development offering? Fantastic.
Send us your name and email, one of our team members will get back to you promptly, answer any questions you may have, share the breath of services we offer, share the love and commitment we have to deliver timely and of the highest quality.
Why Us?
Human Touch
Smiling and being friendly is so important.
“People have forgotten what the human touch is, what it is to smile, for somebody to smile at them, somebody to recognize them, somebody to wish them well. The terrible thing is to be unwanted.”
– Mother Teresa –
We are open, friendly and responsive!
Passionately Resolute
We are driven by passion, seized by obsession, delighted by creation, enthralled with expression, entranced by vision, diverted by daydreams, filled with emotion, fueled by compulsion, consumed with beauty, and blindsided by inspiration.
Welcome to our minds!
Broad Capability
We are a young and vigorous team with broad expertise and global experience.
We draw on this broad expertise to accentuate and add value to the range of services we offer in the relevant friends we cover, i.e. Business Intelligence and driving Digital Transformation.
We cover areas such artificial intelligence, cyber security, business and data analysis, reporting, team leading, project management, DB experts, business, data, and enterprise architecture, general, web, and application development, business and personal coaching, cloud, sales and marketing, financial, HR, and more.
Global Experience
Our top echelon has practical IT experience of living and working in various countries around the world, such as Portugal, Brazil, South Africa, United States, UK, Germany, Netherlands, Belgium, Switzerland, Oman, Hong Kong, Singapore, Taipei, among others.
This global experience allows us to be more flexible, faster at adapting and delivering.
Multi Language Support
All our support is offered in English and Portuguese.
We offer limited support in Spanish, French, German and Dutch.
Companies need to remain competitive by ensuring their resources and business processes are collaborating effectively while reducing costs and improving the efficiency of its business.
Our focus is helping you uncover opportunities and overcome challenges within your resourcing, projects, solutions and business operations.
We have the know-how to help pinpoint critical issues and address them through improving the gap between company, people, processes and technology.
Why Scorpion Circle? Because your passion is our passion!
Phone | WhatsApp

Hours
Monday-Thursday
9am - 6pm

Copyright © 2023 Scorpion Circle Ltd. All rights reserved.
Proudly sponsoring a global COVID-19 blog | Web design by HVidal